Resilience Foundry — Continuous Cyber Resilience Platform
See your attack surface the way adversaries do.
Prioritise the exposures attackers will exploit. Validate whether controls work in practice. Give leadership defensible evidence of resilience.
For CISOs, security assurance leaders, and red teams who need confidence, control, and clarity — not another annual report.
In your 30-minute strategy session, you'll:
Attack-path simulation, exposure context, and validation status — in one view.
The real value: reduced uncertainty
Know where attackers are most likely to win
Not just where vulnerabilities exist
Validate assumptions before attackers do
Proof over theory
Give leadership evidence, not confidence theater
Defensible reporting
The Problem with Point-in-Time Assurance
Most organisations still manage cyber resilience through disconnected motions that fail to connect threat intelligence, assessment, and validation into one operating workflow.
Fragmented Assurance Activities
Threat intelligence, vulnerability assessment, exposure management, and security testing are bought and run separately with no connected view.
Point-in-Time Rather Than Continuous
Security assessments remain periodic snapshots while the threat landscape moves continuously, increasing risk exposure.
Intelligence Rarely Drives Action
CTI and contextualisation seldom translate directly into prioritisation, assurance activities, or operational security decisions.
No Unified Reporting
Boards and regulators demand evidence of resilience, yet most teams stitch together slides from five different tools to tell one story.
One Continuous Resilience Workflow
Discover threats, assess risk in context, validate what's real.
Each output feeds back into the next, creating a continuous assurance loop.
Discover
Know which threats, actors, and exposures are most relevant to your environment — not generic feeds.
- Relevant threats surfaced
- External exposures mapped
- Adversary tradecraft identified
You get: A prioritised threat and exposure landscape specific to your organisation
Assess
Understand which exposures matter most through realistic attack-path analysis and contextual risk scoring.
- Realistic attack paths modelled
- Gaps mapped to MITRE ATT&CK
- Risk prioritised by exploitability
You get: Clear prioritisation of what to test and what to fix first
Validate
Prove whether risks are exploitable and whether controls actually work — not theoretical assumptions.
- Control effectiveness tested
- Detection rules generated
- Remediation verified
You get: Evidence of what's defended and what needs action
From Fragmented Assurance to Continuous Resilience
See what changes when discovery, assessment, and validation work as one connected workflow.
Before: Siloed Assurance
- Annual pen tests that age within weeks
- CTI feeds that never reach testing teams
- Remediation lists no one can prioritise
- Board slides stitched from five tools
After: Resilience Foundry
- Continuous visibility into real exposures
- Prioritised attack paths worth testing
- Validated control effectiveness with evidence
- Unified resilience reporting in one click
Faster
threat-to-test prioritisation
Fewer
wasted testing cycles
Stronger
board and regulator reporting
Clearer
remediation decisions
What Makes Resilience Foundry Different
What We Unify
- Threat intelligence and exposure management
- Contextual risk assessment
- Continuous security validation
- Board-ready resilience reporting
What Others Leave Disconnected
- Separate CTI subscriptions
- Standalone vulnerability scanners
- Annual pen test engagements
- Manual report aggregation
Why It Matters
- Intelligence actually drives testing
- Prioritisation based on real exploitability
- Continuous evidence, not annual snapshots
- One source of truth for leadership
“The continuous feedback loop between discovery, assessment, and validation has fundamentally changed how we approach resilience. We're no longer guessing about our security posture — we're measuring it.”
Security Leader
Enterprise Financial Services
How It Works
Answers to the practical questions: deployment, integration, and time to value.
SaaS Platform
Cloud-hosted with no agents required. Connects to your environment via secure integrations and API access.
Works With Your Stack
Integrates with existing vulnerability scanners, SIEM, and threat feeds. Adds context and validation — doesn't replace.
For Security Teams
Used daily by security analysts, red teamers, and assurance leads. Board-ready reporting for leadership.
Fast Time to Value
Scoped assessment and initial configuration in week one. Actionable outputs within two weeks of onboarding.
Why Siloed Assurance Fails
Point-in-time testing and disconnected tools create dangerous gaps between confidence and reality. The data exposes a consistent failure to connect discovery, assessment, and validation into one operating workflow.
Confidence Is Not Readiness
Intelligence Stays Siloed
Discovery Without Context
The Threat Landscape Moves Faster
Cyber resilience fails not from lack of effort, but because discovery, assessment, and validation remain disconnected motions instead of one continuous workflow.
(Sources: IBM, Gartner, SANS, Ponemon, Mandiant, ENISA)
No commitment required
Why Trust Resilience Foundry
Built by Security Operators
Practitioner-Led
Founded by security professionals with enterprise red team and assurance backgrounds.
Enterprise Security
Designed for regulated industries. Data handling and access controls built for enterprise requirements.
Secure by Design
Encryption in transit and at rest. Audit logging. Compliance-ready architecture.
Direct Support
Named contact. Implementation ownership. Response model designed for security teams.
Common Questions
Answers to what security leaders typically ask before evaluating the platform.
CISOs, security assurance leaders, and red teams in organisations that need continuous visibility into their real risk posture — not just annual snapshots. Particularly relevant for financial services, critical infrastructure, and regulated industries facing DORA, NIS2, or similar requirements.
Resilience Foundry sits alongside your current stack, not on top of it. We ingest data from your existing vulnerability scanners, SIEM, and threat feeds, then add our own discovery, contextualisation, and validation layers. The goal is to connect what you already have — not replace it.
We start with a scoped environment assessment to understand your current tooling, threat profile, and assurance gaps. From there, we configure the platform to your context and run an initial discovery-assess-validate cycle. Most organisations see actionable outputs within the first two weeks.
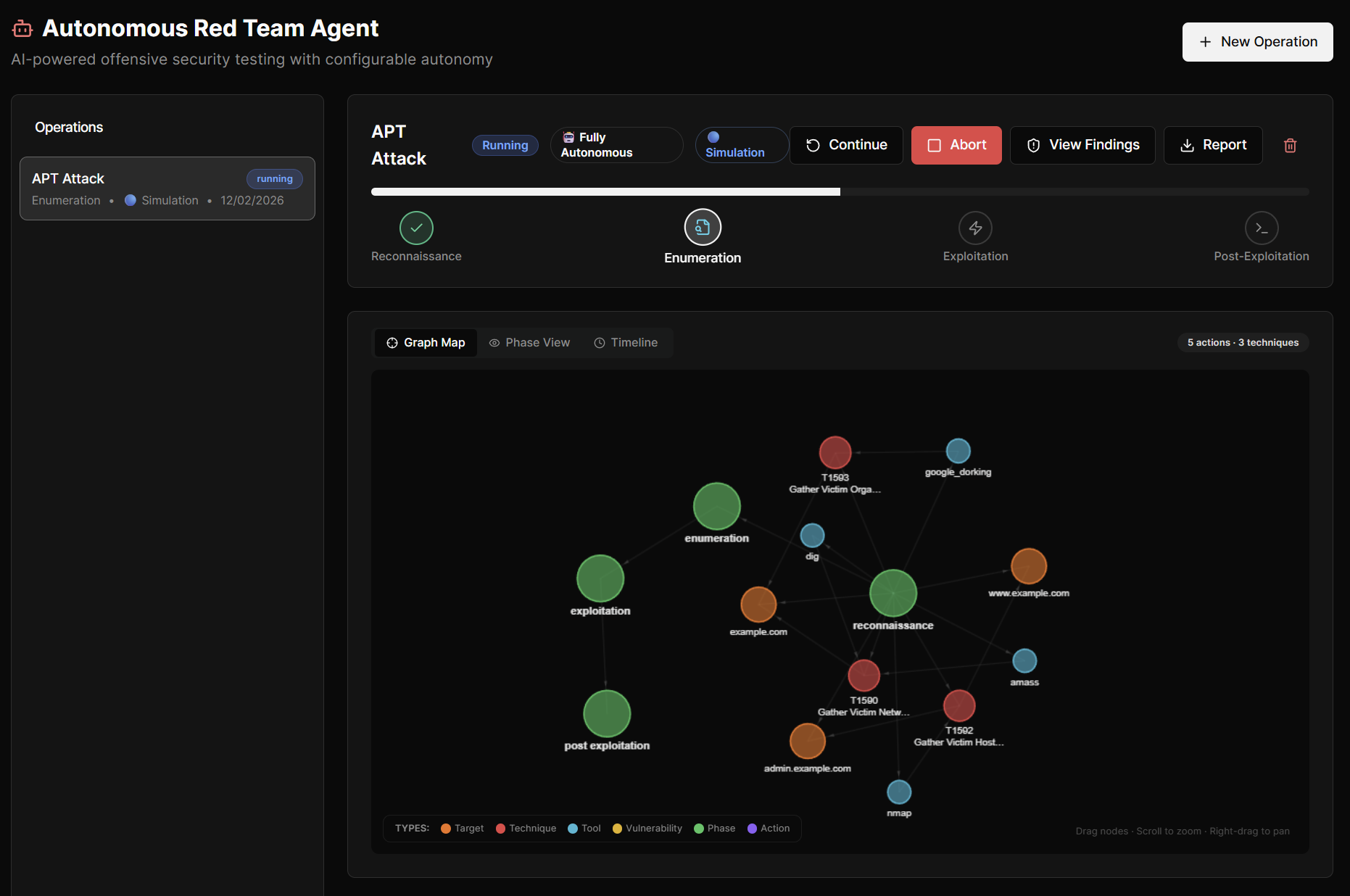
Validation combines AI-powered agentic testing with expert-led assessment. We test prioritised attack paths identified during the Assess phase, measuring whether controls actually detect and block real techniques. Results feed back into continuous discovery.
You get a unified dashboard showing threat exposure, risk prioritisation, and validation status. Board-ready reports can be generated on demand — consolidating findings into one narrative rather than stitching together outputs from multiple tools.
Continuously. Discovery scans run on configurable schedules (quick scans in minutes, deep scans in under an hour). Threat intelligence correlates in real-time. Validation cycles are ongoing, not annual. You always have a current view of your resilience posture.
The platform is designed for enterprise security teams. Data is encrypted in transit and at rest. We operate under strict data handling policies and can accommodate specific compliance requirements. Access controls and audit logging are built in.
The cost of waiting
See Your Assurance Gaps Mapped in 30 Minutes
Get a tailored resilience review based on your current tools, threat profile, and assurance workflow. Leave with clear next steps — whether you choose to move forward or not.
“The strategy session helped us see gaps we didn't know we had. Even before deployment, the insights were valuable.”
— Security Leader, Enterprise Financial Services
Book your resilience review
30-minute strategy session with a security expert. No sales pressure.
Or view platform overview firstFlexible evaluation options after the demo:
Latest Insights
Practical perspectives on building measurable cyber resilience.
Beyond the Checklist: Why Operational Resilience Demands Threat-Led Testing
Traditional penetration testing is no longer enough. Discover why organisations must mature toward Threat Intelligence-Led, Continuous Adversarial Testing to achieve true cyber resilience.
Why Cyber Resilience Must Be Measured, Not Assumed
Most organisations believe they are resilient until an incident proves otherwise. Discover why continuous measurement is the foundation of true cyber resilience.
From Threat Intelligence to Action: Closing the Feedback Loop
Threat intelligence only creates value when it drives action. Learn how to transform raw threat data into operational improvements.
Ready to move from insight to action?
Explore the Platform